Offline Ransomware Encrypts Your Data without C&C Comms
Por um escritor misterioso
Descrição
Early in September, Check Point obtained a sample of a ransomware. When the sample was run, the following message, written in Russian, appeared:
Ransomware Redefined: RedEnergy Stealer-as-a-Ransomware
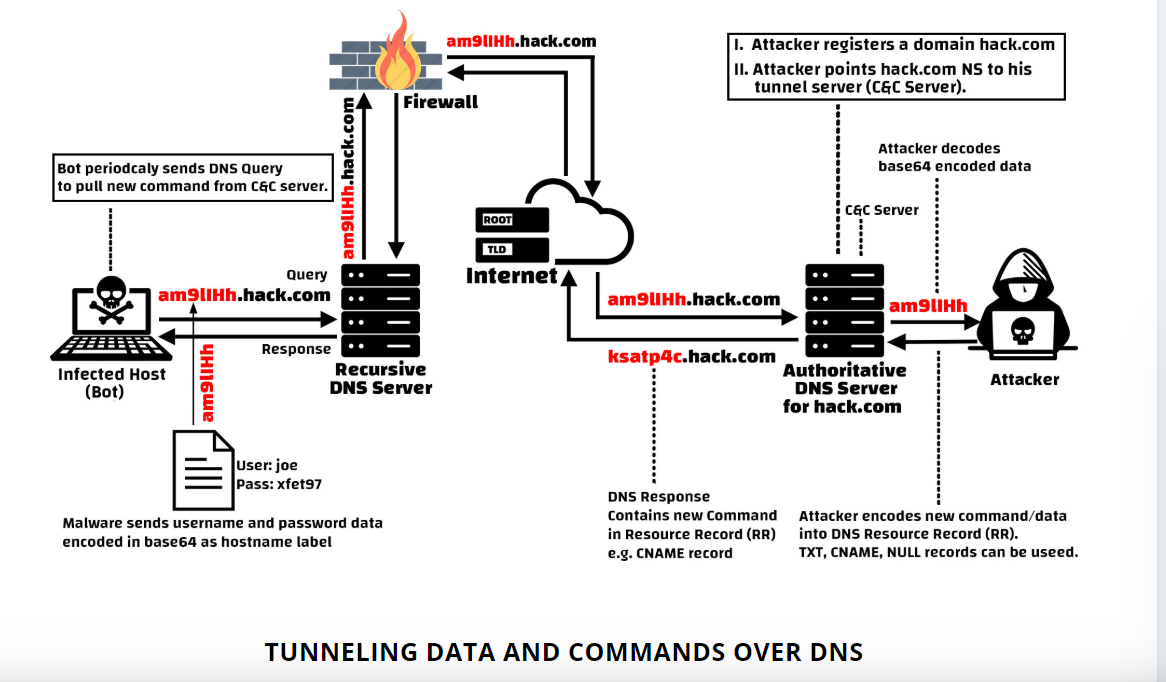
Obtain C&C Channel. Command and Control is a key role to…, by Mohan reddy, Redteam & Blueteam Series
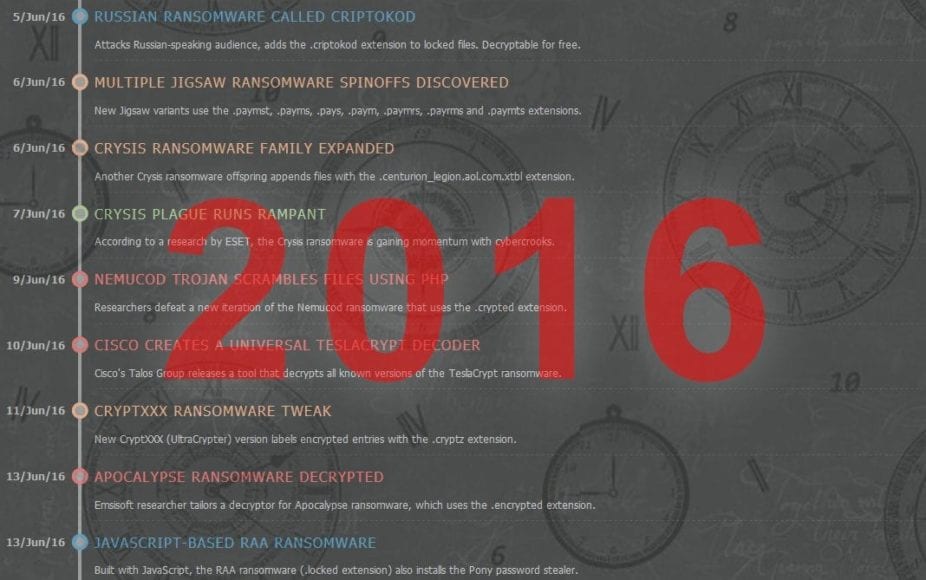
Ransomware Chronicle 2016 - Privacy PC

Ransomware Realities: Exploring the Risks to Hybrid Cloud Solutions - RedSeal

The real cost of ransomware: Attacks take most victims offline for at least a week
What is C2? Command and Control Infrastructure Explained
Hackers use SystemBC Malware to Hide C&C Server Communication

Sodinokibi Ransomware: Still Very Relevant for MSSPs
ChChes – Malware that Communicates with C&C Servers Using Cookie Headers - JPCERT/CC Eyes

Applied Sciences, Free Full-Text
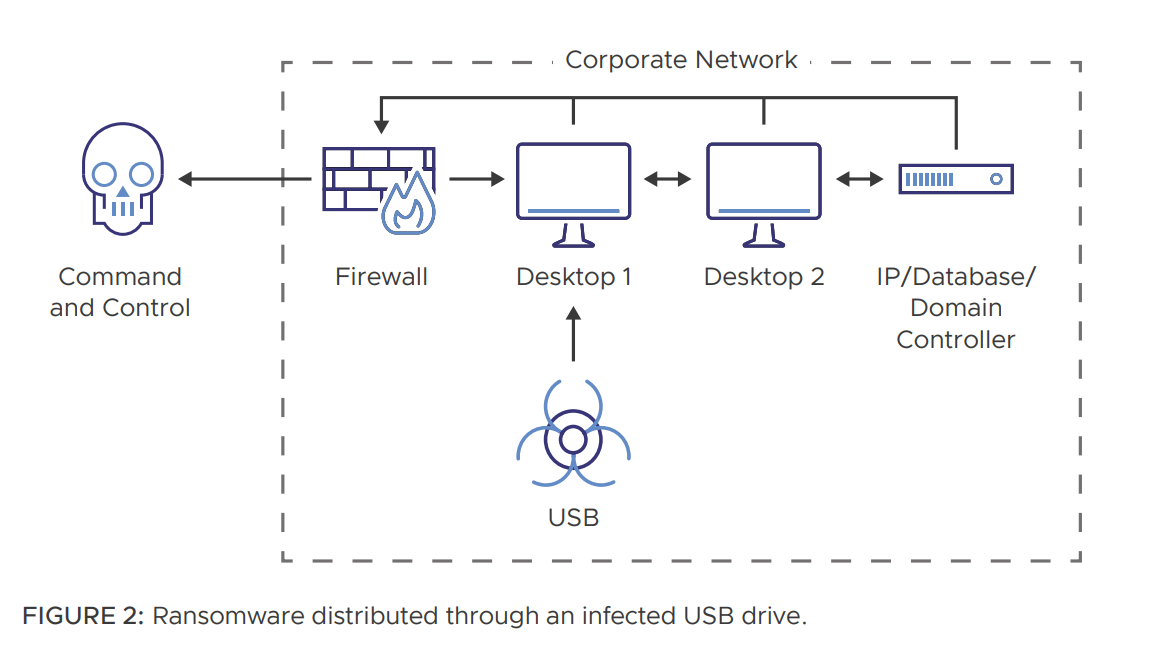
Ransomware Defense in Depth Strategy - Best Practices for Building a Strong Prevention

Ransomware Now Gunning for Your Web Sites – Krebs on Security
de
por adulto (o preço varia de acordo com o tamanho do grupo)