The Evolution of ShellBot Malware: A Dive into Hexadecimal Notation
Por um escritor misterioso
Descrição
Threat actors are constantly innovating to stay one step ahead. One such innovation is the use of hexadecimal notation in the distribution of ShellBot malware. AhnLab Security Emergency Response Center (ASEC) recently reported a shift in the tactics employed by cybercriminals to distribute ShellBot, a DDoS malware targeting Linux SSH
Threat actors are constantly innovating to stay one step ahead. One such innovation is the use of hexadecimal notation in the distribution of ShellBot malware. AhnLab Security Emergency Response Center (ASEC) recently reported a shift in the tactics employed by cybercriminals to distribute ShellBot, a DDoS malware targeting Linux SSH servers. Let's delve into the nitty-gritty of this development, shall we? The Old Ways: Dot-Decimal Notation Traditionally, ShellBot was distributed using IP addr
Threat actors are constantly innovating to stay one step ahead. One such innovation is the use of hexadecimal notation in the distribution of ShellBot malware. AhnLab Security Emergency Response Center (ASEC) recently reported a shift in the tactics employed by cybercriminals to distribute ShellBot, a DDoS malware targeting Linux SSH servers. Let's delve into the nitty-gritty of this development, shall we? The Old Ways: Dot-Decimal Notation Traditionally, ShellBot was distributed using IP addr

ShellBot DDoS Malware Installed Through Hexadecimal Notation Addresses - ASEC BLOG
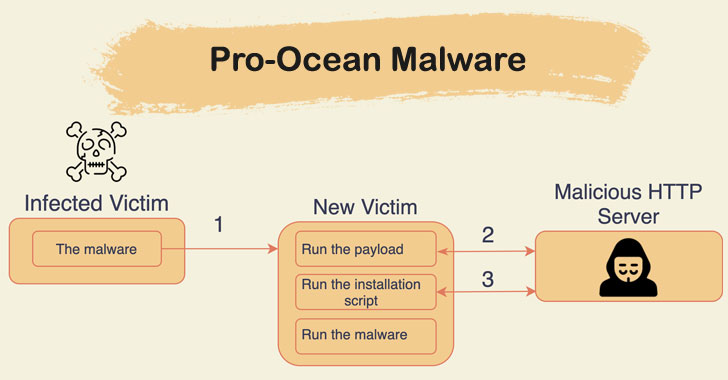
New Cryptojacking Malware Targeting Apache, Oracle, Redis Se - vulnerability database

The Anomali Blog
Threat Intel Reports
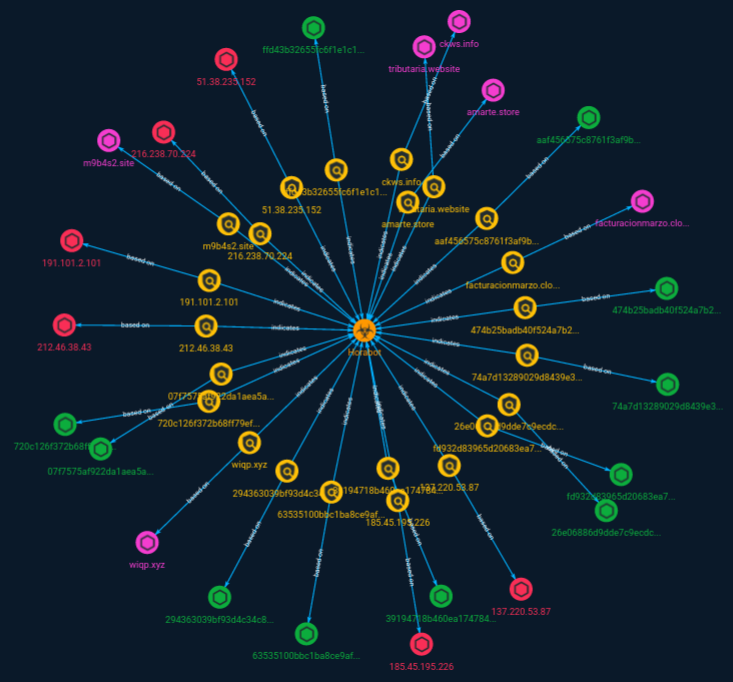
QakBot Malware Group Increases Command and Control Network with Additional 15 New Servers

Analysis Report on Lazarus Threat Group's Volgmer and Scout Malware - ASEC BLOG

ShellBot uses hexadecimal notation to infiltrate Linux SSH servers., CyberCureME - Cyber Security Marketplace posted on the topic

ShellBot Malware Being Distributed to Linux SSH Servers - ASEC BLOG

PDF) A Near Real-Time Scheme for Collecting and Analyzing IoT Malware Artifacts at Scale

Dimitris Alevizos on LinkedIn: #cisa #cybersecurity #threats #vulnerabilities #attacks #investments…

New Android Malware Steals Crypto Credentials Using uses OCR

DXC Security Threat Intelligence Report
RST TI Report Digest: 16 Oct 2023, by RST Cloud, Oct, 2023

Emotet (Malware Family)
de
por adulto (o preço varia de acordo com o tamanho do grupo)