Hackers Using New Obfuscation Mechanisms to Evade Detection
Por um escritor misterioso
Descrição
Recently, Microsoft has unveiled details of a deceptive social engineering campaign, in which the operators proceeded to change their obfuscation

Cyble Detects STRRAT Version 1.6 Using Dual String Obfuscation
ITG23 Crypters Highlight Cooperation Between Cybercriminal Groups
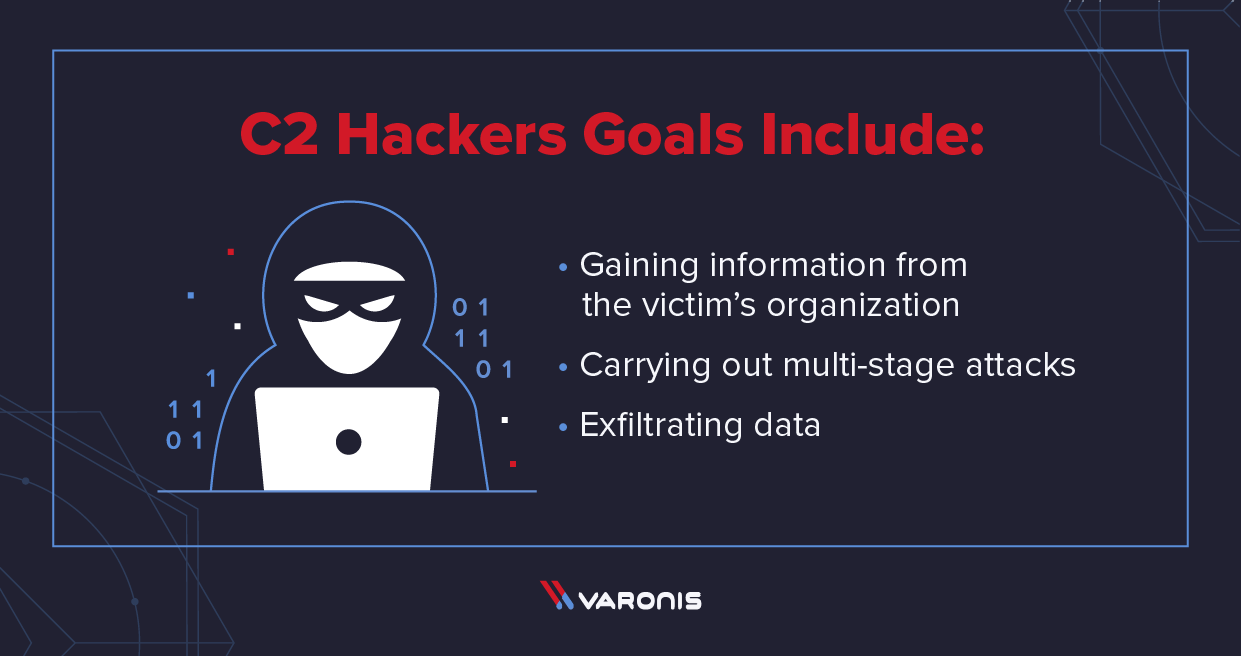
What is C2? Command and Control Infrastructure Explained

Locky Ransomware Actors Turning To XORed JavaScript

Code obfuscation - Cybersecurity ASEE
Threat Actors Using Obfuscation in Attempt to Evade Detection

Google ads push 'virtualized' malware made for antivirus evasion
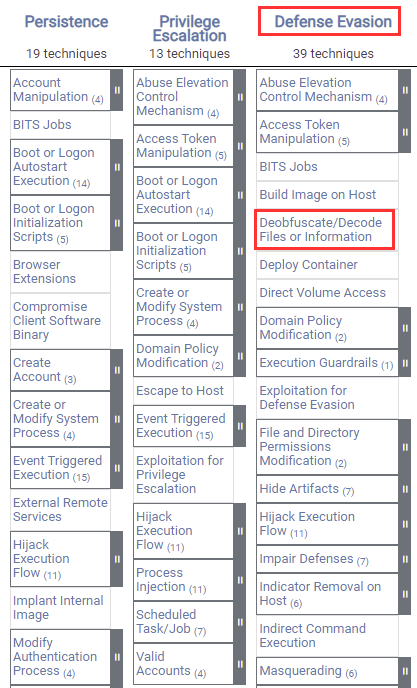
Windows Red Team Defense Evasion Techniques

Know your Malware - A Beginner's Guide to Encoding Techniques Used
de
por adulto (o preço varia de acordo com o tamanho do grupo)