Towards an Automated Process to Categorise Tor's Hidden Services
Por um escritor misterioso
Descrição

Hidden Services- Tor hidden Services - BitcoinWiki

Figure 1 from Application-level attack against Tor's hidden service
Tor: Anonymity For Better or For Worse, by Leo Goldberg, Systems and Network Security

Dark Web Alerts: Identifying Criminal Data Exposure on the Dark Web - Flare
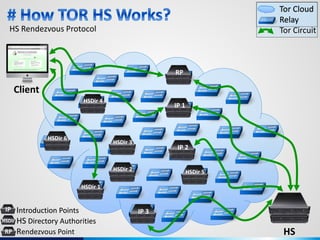
Are TOR Hidden Services really hidden? Demystifying HS Directory surveillance by injecting Decoys inside TOR!

Threat-Hunting for Identity Threats in Snowflake

E-Book: HOW TO SETUP TOR HIDDEN SERVICES
TOR Fronting — Utilising Hidden Services to Hide Attack Infrastructure, by Vincent Yiu

The foundation and architecture of precision medicine in neurology and psychiatry: Trends in Neurosciences

Journal of Automation, Mobile Robotics and Intelligent Systems, vol. 16, no. 4 (2022) by Ł-PIAP - Issuu

The rise of website fingerprinting on Tor: Analysis on techniques and assumptions - ScienceDirect
De-anonymization of Tor Hidden Services With 88 Percent Certainty, Researchers Say

A deep learning‐based framework to identify and characterise heterogeneous secure network traffic - Islam - 2023 - IET Information Security - Wiley Online Library

How to Install Tor Browser on Linux Mint - Linux Genie

How Cybercriminals are using Blockchain DNS: From the Market to the .Bazar - ReliaQuest
de
por adulto (o preço varia de acordo com o tamanho do grupo)